Ms12-021 Patch Download
F22 adf patch download. F22:ADF - Patch Preview. To download the patch click HERE. As many of you know, DiD have increased both ground detail AND frame rate under both Glide and Direct3d. And under V2 this thing REALLY flies! F-22 ADF Multi-player and Communications.
- Ms12-021 Patch Downloads
- Amtemu V0.9.2 Patch Download
- Ms12-021 Patch Download Torrent
- Pes Patch Download
- Game Patch Download
Administrators who run a Windows server will want to download the patch from MS12-017 which addresses a DoS vulnerability in Windows Server's DNS service. Developers should take note of MS12-021, which describes and fixes a privilege escalation vulnerability when loading plugins in Visual Studio. LANDesk Patch News Bulletin: Microsoft has Released its Patch Tuesday Bulletins for March 2012. You can run the tool from this Web page anytime.
-->Security Bulletin
Vulnerability in Visual Studio Could Allow Elevation of Privilege (2651019)
Published: March 13, 2012
Version: 1.0
General Information
Executive Summary
This security update resolves one privately reported vulnerability in Visual Studio. The vulnerability could allow elevation of privilege if an attacker places a specially crafted add-in in the path used by Visual Studio and convinces a user with higher privileges to start Visual Studio. An attacker must have valid logon credentials and be able to log on locally to exploit this vulnerability. The vulnerability could not be exploited remotely or by anonymous users.
This security update is rated Important for all supported editions of Microsoft Visual Studio 2008 and Microsoft Visual Studio 2010. For more information, see the subsection, Affected and Non-Affected Software, in this section.
The security update addresses the vulnerability by correcting the manner in which Visual Studio restricts where add-ins are loaded. For more information about the vulnerability, see the Frequently Asked Questions (FAQ) subsection for the specific vulnerability entry under the next section, Vulnerability Information.
Recommendation. The majority of customers have automatic updating enabled and will not need to take any action because this security update will be downloaded and installed automatically. Customers who have not enabled automatic updating need to check for updates and install this update manually. For information about specific configuration options in automatic updating, see Microsoft Knowledge Base Article 294871.
For administrators and enterprise installations, or end users who want to install this security update manually, Microsoft recommends that customers apply the update at the earliest opportunity using update management software, or by checking for updates using the Microsoft Update service.
See also the section, Detection and Deployment Tools and Guidance, later in this bulletin.
Feb 26, 2016 Stardew Valley is an open-ended country-life RPG. This update has lot of added contents. Note: Installing the latest version from the previous version will never affect your progress/save file. (GOG version). STEAM version will be fine aswell since it. https://monkeysnin.netlify.app/stardew-valley-v1218-patch-download.html. Windows 7 / 8 / 10, 2 Ghz, 2 GB RAM, 256 MB video memory, shader model 3.0+, Version 10, 500 MB avai. Description You’ve inherited your grandfather’s old farm plot in Stardew Valley. Stardew Valley Free Download PC Game Cracked in Direct Link and Torrent. Stardew Valley is a simulation game. Stardew Valley PC Game Overview: Stardew Valley is developed by ConcernedApe and published by Chucklefish. It was released in 27 Apr, 2017. You’ve inherited your grandfather’s old farm plot in Stardew Valley. Stardew Valley free. download full Version For Pc. So Finaly after reading the whole information about the game now do stardew valley download it is the 100% free link so you do not have to pay anything to play full version of game. Download Here. Once Stardew Valley is done downloading, right click the.zip file and click on “Extract to Stardew.Valley.v1.3.25.zip” (To do this you must have WinRAR, which you can get here). Double click inside the Stardew Valley folder and run the exe application.
Known Issues.Microsoft Knowledge Base Article 2651019 documents the currently known issues that customers may experience when installing this security update. The article also documents recommended solutions for these issues.
Affected and Non-Affected Software
The following software have been tested to determine which versions or editions are affected. Other versions or editions are either past their support life cycle or are not affected. To determine the support life cycle for your software version or edition, visit Microsoft Support Lifecycle.
Ms12-021 Patch Downloads
Affected Software
| Software | Maximum Security Impact | Aggregate Severity Rating | Bulletins Replaced by this Update |
|---|---|---|---|
| Microsoft Visual Studio 2008 Service Pack 1 (KB2669970) | Elevation of Privilege | Important | None |
| Microsoft Visual Studio 2010 (KB2644980) | Elevation of Privilege | Important | None |
| Microsoft Visual Studio 2010 Service Pack 1 (KB2645410) | Elevation of Privilege | Important | None |
| Affected Software | Visual Studio Add-In Vulnerability - CVE-2012-0008 | Aggregate Severity Rating |
|---|---|---|
| Microsoft Visual Studio 2008 Service Pack 1 | Important Elevation of Privilege | Important |
| Microsoft Visual Studio 2010 | Important Elevation of Privilege | Important |
| Microsoft Visual Studio 2010 Service Pack 1 | Important Elevation of Privilege | Important |
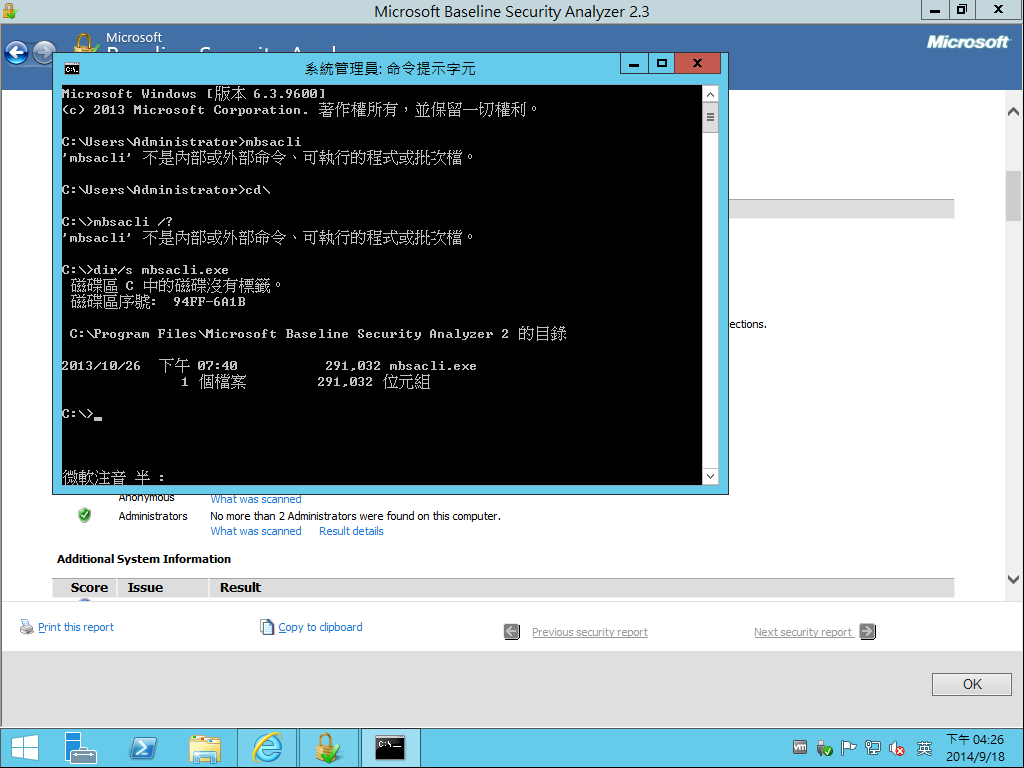
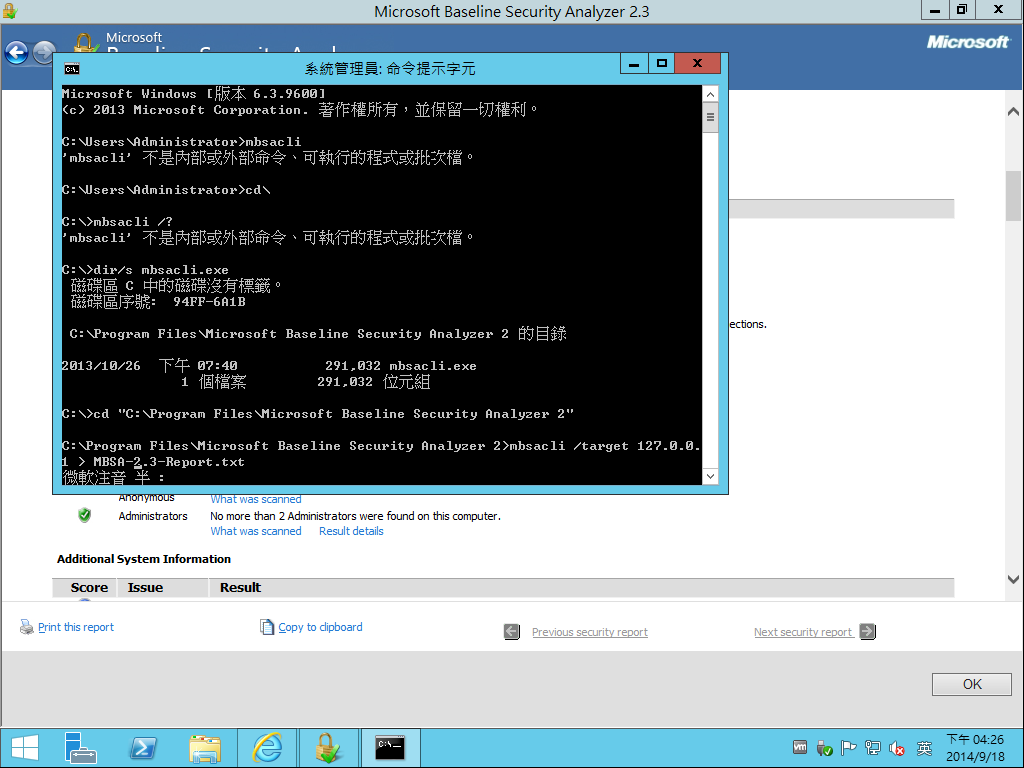
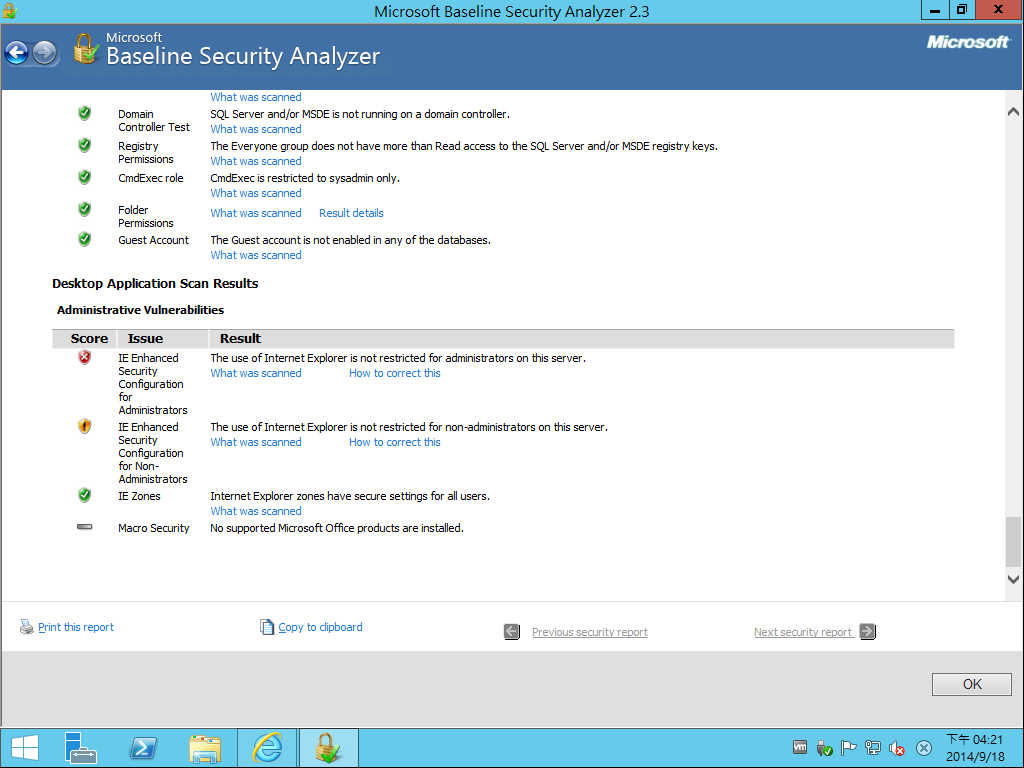 Visual Studio Add-In Vulnerability - CVE-2012-0008 -------------------------------------------------- An elevation of privilege vulnerability exists in Visual Studio due to the insecure loading of add-ins from within Visual Studio. An attacker who successfully exploited this vulnerability could run arbitrary code with elevated privileges. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. To view this vulnerability as a standard entry in the Common Vulnerabilities and Exposures list, see [CVE-2012-0008](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2012-0008). #### Mitigating Factors for Visual Studio Add-In Vulnerability - CVE-2012-0008 Mitigation refers to a setting, common configuration, or general best-practice, existing in a default state, that could reduce the severity of exploitation of a vulnerability. The following mitigating factors may be helpful in your situation: - An attacker must have valid logon credentials and be able to log on locally to exploit this vulnerability. The vulnerability could not be exploited remotely or by anonymous users. #### Workarounds for Visual Studio Add-In Vulnerability - CVE-2012-0008 Microsoft has not identified any workarounds for this vulnerability. #### FAQ for Visual Studio Add-In Vulnerability - CVE-2012-0008 **What is the scope of the vulnerability?** This is an elevation of privilege vulnerability. An attacker who successfully exploited this vulnerability could execute arbitrary code and take complete control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. **What causes the vulnerability?** This vulnerability is caused by Visual Studio loading add-ins from insecure file locations. **What is** **a Visual Studio** **add-in?** Visual Studio add-ins implement an extensibility interface within Visual Studio for customizing and automating the interactive development environment (IDE). Developers choose to automate the Visual Studio IDE to increase their productivity. As developers create more and more applications, they may find themselves spending more time doing redundant project setup and configuration. Add-ins help developers cut out redundancy and allow them to focus on core development tasks. Developers can take this mundane set of steps out of the process by using a combination of add-ins, macros, and templates. For more information about Visual Studio add-ins, see the MSDN article, [Creating Visual Studio Add-Ins](http://msdn.microsoft.com/en-us/vstudio/bb968855). **What might an attacker use the vulnerability to do?** An attacker who successfully exploited this vulnerability could run arbitrary code with elevated privileges. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. **How could an attacker exploit the** **vulnerability?** To exploit this vulnerability, an attacker would first have to log on to the system. An attacker could then place a specially crafted add-in in the path used by Visual Studio. When Visual Studio is started by an administrator, the specially crafted add-in would be loaded with the same privileges as the administrator. **What systems are primarily at risk from the vulnerability?** Systems where Microsoft Visual Studio is used for development, including workstations and terminal servers, are primarily at risk. Servers could be at more risk if administrators allow users to log on to servers and to run programs. However, best practices strongly discourage allowing this. **What does the update do?** The update addresses this vulnerability by correcting the manner in which Visual Studio restricts where add-ins are loaded. **When this security bulletin was issued, had this vulnerability been publicly disclosed?** No. Microsoft received information about this vulnerability through coordinated vulnerability disclosure. **When this security bulletin was issued, had Microsoft received any reports that this vulnerability was being exploited?** No. Microsoft had not received any information to indicate that this vulnerability had been publicly used to attack customers when this security bulletin was originally issued. ### Update Information Detection and Deployment Tools and Guidance ------------------------------------------- **Security Central** Manage the software and security updates you need to deploy to the servers, desktop, and mobile systems in your organization. For more information see the [TechNet Update Management Center](http://go.microsoft.com/fwlink/?linkid=69903). The [Microsoft TechNet Security website](http://go.microsoft.com/fwlink/?linkid=21132) provides additional information about security in Microsoft products. Security updates are available from [Microsoft Update](http://go.microsoft.com/fwlink/?linkid=40747) and [Windows Update](http://go.microsoft.com/fwlink/?linkid=21130). Security updates are also available from the [Microsoft Download Center](http://go.microsoft.com/fwlink/?linkid=21129). You can find them most easily by doing a keyword search for 'security update.' Finally, security updates can be downloaded from the [Microsoft Update Catalog](http://go.microsoft.com/fwlink/?linkid=96155). The Microsoft Update Catalog provides a searchable catalog of content made available through Windows Update and Microsoft Update, including security updates, drivers and service packs. By searching using the security bulletin number (such as, 'MS07-036'), you can add all of the applicable updates to your basket (including different languages for an update), and download to the folder of your choosing. For more information about the Microsoft Update Catalog, see the [Microsoft Update Catalog FAQ](http://go.microsoft.com/fwlink/?linkid=97900). **Detection and Deployment Guidance** Microsoft provides detection and deployment guidance for security updates. This guidance contains recommendations and information that can help IT professionals understand how to use various tools for detection and deployment of security updates. For more information, see [Microsoft Knowledge Base Article 961747](http://support.microsoft.com/kb/961747). **Microsoft Baseline Security Analyzer** Microsoft Baseline Security Analyzer (MBSA) allows administrators to scan local and remote systems for missing security updates as well as common security misconfigurations. For more information about MBSA, visit [Microsoft Baseline Security Analyzer](http://www.microsoft.com/technet/security/tools/mbsahome.mspx). The following table provides the MBSA detection summary for this security update. | Software | MBSA | |---------------------------------------------|------| | Microsoft Visual Studio 2008 Service Pack 1 | Yes | | Microsoft Visual Studio 2010 | Yes | | Microsoft Visual Studio 2010 Service Pack 1 | Yes | **Note** For customers using legacy software not supported by the latest release of MBSA, Microsoft Update, and Windows Server Update Services, please visit [Microsoft Baseline Security Analyzer](http://www.microsoft.com/technet/security/tools/mbsahome.mspx) and reference the Legacy Product Support section on how to create comprehensive security update detection with legacy tools. **Windows Server Update Services** Windows Server Update Services (WSUS) enables information technology administrators to deploy the latest Microsoft product updates to computers that are running the Windows operating system. For more information about how to deploy security updates using Windows Server Update Services, see the TechNet article, [Windows Server Update Services](http://technet.microsoft.com/en-us/wsus/default.aspx). **Systems Management Server** The following table provides the SMS detection and deployment summary for this security update. | Software | SMS 2003 with ITMU | Configuration Manager 2007 | |---------------------------------------------|--------------------|----------------------------| | Microsoft Visual Studio 2008 Service Pack 1 | Yes | Yes | | Microsoft Visual Studio 2010 | Yes | Yes | | Microsoft Visual Studio 2010 Service Pack 1 | Yes | Yes | **Note** Microsoft discontinued support for SMS 2.0 on April 12, 2011. For SMS 2003, Microsoft also discontinued support for the Security Update Inventory Tool (SUIT) on April 12, 2011. Customers are encouraged to upgrade to [System Center Configuration Manager 2007](http://technet.microsoft.com/en-us/library/bb735860.aspx). For customers remaining on SMS 2003 Service Pack 3, the [Inventory Tool for Microsoft Updates](http://technet.microsoft.com/en-us/sms/bb676783.aspx) (ITMU) is also an option. For SMS 2003, the SMS 2003 Inventory Tool for Microsoft Updates (ITMU) can be used by SMS to detect security updates that are offered by [Microsoft Update](http://go.microsoft.com/fwlink/?linkid=40747) and that are supported by [Windows Server Update Services](http://go.microsoft.com/fwlink/?linkid=50120). For more information about the SMS 2003 ITMU, see [SMS 2003 Inventory Tool for Microsoft Updates](http://technet.microsoft.com/en-us/sms/bb676783.aspx). For more information about SMS scanning tools, see [SMS 2003 Software Update Scanning Tools](http://technet.microsoft.com/en-us/sms/bb676786.aspx). See also [Downloads for Systems Management Server 2003](http://technet.microsoft.com/en-us/sms/bb676766.aspx). System Center Configuration Manager 2007 uses WSUS 3.0 for detection of updates. For more information about Configuration Manager 2007 Software Update Management, visit [System Center Configuration Manager 2007](http://technet.microsoft.com/en-us/library/bb735860.aspx). For more information about SMS, visit the [SMS website](http://go.microsoft.com/fwlink/?linkid=21158). For more detailed information, see [Microsoft Knowledge Base Article 910723](http://support.microsoft.com/kb/910723): Summary list of monthly detection and deployment guidance articles. **Update Compatibility Evaluator and Application Compatibility Toolkit** Updates often write to the same files and registry settings required for your applications to run. This can trigger incompatibilities and increase the time it takes to deploy security updates. You can streamline testing and validating Windows updates against installed applications with the [Update Compatibility Evaluator](http://technet2.microsoft.com/windowsvista/en/library/4279e239-37a4-44aa-aec5-4e70fe39f9de1033.mspx?mfr=true) components included with [Application Compatibility Toolkit](http://www.microsoft.com/downloads/details.aspx?familyid=24da89e9-b581-47b0-b45e-492dd6da2971&displaylang=en). The Application Compatibility Toolkit (ACT) contains the necessary tools and documentation to evaluate and mitigate application compatibility issues before deploying Windows Vista, a Windows Update, a Microsoft Security Update, or a new version of Windows Internet Explorer in your environment. Security Update Deployment -------------------------- **Affected Software** For information about the specific security update for your affected software, click the appropriate link: #### Microsoft Visual Studio 2008 Service Pack 1 **Reference Table** The following table contains the security update information for this software. You can find additional information in the subsection, **Deployment Information**, in this section.
Visual Studio Add-In Vulnerability - CVE-2012-0008 -------------------------------------------------- An elevation of privilege vulnerability exists in Visual Studio due to the insecure loading of add-ins from within Visual Studio. An attacker who successfully exploited this vulnerability could run arbitrary code with elevated privileges. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. To view this vulnerability as a standard entry in the Common Vulnerabilities and Exposures list, see [CVE-2012-0008](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2012-0008). #### Mitigating Factors for Visual Studio Add-In Vulnerability - CVE-2012-0008 Mitigation refers to a setting, common configuration, or general best-practice, existing in a default state, that could reduce the severity of exploitation of a vulnerability. The following mitigating factors may be helpful in your situation: - An attacker must have valid logon credentials and be able to log on locally to exploit this vulnerability. The vulnerability could not be exploited remotely or by anonymous users. #### Workarounds for Visual Studio Add-In Vulnerability - CVE-2012-0008 Microsoft has not identified any workarounds for this vulnerability. #### FAQ for Visual Studio Add-In Vulnerability - CVE-2012-0008 **What is the scope of the vulnerability?** This is an elevation of privilege vulnerability. An attacker who successfully exploited this vulnerability could execute arbitrary code and take complete control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. **What causes the vulnerability?** This vulnerability is caused by Visual Studio loading add-ins from insecure file locations. **What is** **a Visual Studio** **add-in?** Visual Studio add-ins implement an extensibility interface within Visual Studio for customizing and automating the interactive development environment (IDE). Developers choose to automate the Visual Studio IDE to increase their productivity. As developers create more and more applications, they may find themselves spending more time doing redundant project setup and configuration. Add-ins help developers cut out redundancy and allow them to focus on core development tasks. Developers can take this mundane set of steps out of the process by using a combination of add-ins, macros, and templates. For more information about Visual Studio add-ins, see the MSDN article, [Creating Visual Studio Add-Ins](http://msdn.microsoft.com/en-us/vstudio/bb968855). **What might an attacker use the vulnerability to do?** An attacker who successfully exploited this vulnerability could run arbitrary code with elevated privileges. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. **How could an attacker exploit the** **vulnerability?** To exploit this vulnerability, an attacker would first have to log on to the system. An attacker could then place a specially crafted add-in in the path used by Visual Studio. When Visual Studio is started by an administrator, the specially crafted add-in would be loaded with the same privileges as the administrator. **What systems are primarily at risk from the vulnerability?** Systems where Microsoft Visual Studio is used for development, including workstations and terminal servers, are primarily at risk. Servers could be at more risk if administrators allow users to log on to servers and to run programs. However, best practices strongly discourage allowing this. **What does the update do?** The update addresses this vulnerability by correcting the manner in which Visual Studio restricts where add-ins are loaded. **When this security bulletin was issued, had this vulnerability been publicly disclosed?** No. Microsoft received information about this vulnerability through coordinated vulnerability disclosure. **When this security bulletin was issued, had Microsoft received any reports that this vulnerability was being exploited?** No. Microsoft had not received any information to indicate that this vulnerability had been publicly used to attack customers when this security bulletin was originally issued. ### Update Information Detection and Deployment Tools and Guidance ------------------------------------------- **Security Central** Manage the software and security updates you need to deploy to the servers, desktop, and mobile systems in your organization. For more information see the [TechNet Update Management Center](http://go.microsoft.com/fwlink/?linkid=69903). The [Microsoft TechNet Security website](http://go.microsoft.com/fwlink/?linkid=21132) provides additional information about security in Microsoft products. Security updates are available from [Microsoft Update](http://go.microsoft.com/fwlink/?linkid=40747) and [Windows Update](http://go.microsoft.com/fwlink/?linkid=21130). Security updates are also available from the [Microsoft Download Center](http://go.microsoft.com/fwlink/?linkid=21129). You can find them most easily by doing a keyword search for 'security update.' Finally, security updates can be downloaded from the [Microsoft Update Catalog](http://go.microsoft.com/fwlink/?linkid=96155). The Microsoft Update Catalog provides a searchable catalog of content made available through Windows Update and Microsoft Update, including security updates, drivers and service packs. By searching using the security bulletin number (such as, 'MS07-036'), you can add all of the applicable updates to your basket (including different languages for an update), and download to the folder of your choosing. For more information about the Microsoft Update Catalog, see the [Microsoft Update Catalog FAQ](http://go.microsoft.com/fwlink/?linkid=97900). **Detection and Deployment Guidance** Microsoft provides detection and deployment guidance for security updates. This guidance contains recommendations and information that can help IT professionals understand how to use various tools for detection and deployment of security updates. For more information, see [Microsoft Knowledge Base Article 961747](http://support.microsoft.com/kb/961747). **Microsoft Baseline Security Analyzer** Microsoft Baseline Security Analyzer (MBSA) allows administrators to scan local and remote systems for missing security updates as well as common security misconfigurations. For more information about MBSA, visit [Microsoft Baseline Security Analyzer](http://www.microsoft.com/technet/security/tools/mbsahome.mspx). The following table provides the MBSA detection summary for this security update. | Software | MBSA | |---------------------------------------------|------| | Microsoft Visual Studio 2008 Service Pack 1 | Yes | | Microsoft Visual Studio 2010 | Yes | | Microsoft Visual Studio 2010 Service Pack 1 | Yes | **Note** For customers using legacy software not supported by the latest release of MBSA, Microsoft Update, and Windows Server Update Services, please visit [Microsoft Baseline Security Analyzer](http://www.microsoft.com/technet/security/tools/mbsahome.mspx) and reference the Legacy Product Support section on how to create comprehensive security update detection with legacy tools. **Windows Server Update Services** Windows Server Update Services (WSUS) enables information technology administrators to deploy the latest Microsoft product updates to computers that are running the Windows operating system. For more information about how to deploy security updates using Windows Server Update Services, see the TechNet article, [Windows Server Update Services](http://technet.microsoft.com/en-us/wsus/default.aspx). **Systems Management Server** The following table provides the SMS detection and deployment summary for this security update. | Software | SMS 2003 with ITMU | Configuration Manager 2007 | |---------------------------------------------|--------------------|----------------------------| | Microsoft Visual Studio 2008 Service Pack 1 | Yes | Yes | | Microsoft Visual Studio 2010 | Yes | Yes | | Microsoft Visual Studio 2010 Service Pack 1 | Yes | Yes | **Note** Microsoft discontinued support for SMS 2.0 on April 12, 2011. For SMS 2003, Microsoft also discontinued support for the Security Update Inventory Tool (SUIT) on April 12, 2011. Customers are encouraged to upgrade to [System Center Configuration Manager 2007](http://technet.microsoft.com/en-us/library/bb735860.aspx). For customers remaining on SMS 2003 Service Pack 3, the [Inventory Tool for Microsoft Updates](http://technet.microsoft.com/en-us/sms/bb676783.aspx) (ITMU) is also an option. For SMS 2003, the SMS 2003 Inventory Tool for Microsoft Updates (ITMU) can be used by SMS to detect security updates that are offered by [Microsoft Update](http://go.microsoft.com/fwlink/?linkid=40747) and that are supported by [Windows Server Update Services](http://go.microsoft.com/fwlink/?linkid=50120). For more information about the SMS 2003 ITMU, see [SMS 2003 Inventory Tool for Microsoft Updates](http://technet.microsoft.com/en-us/sms/bb676783.aspx). For more information about SMS scanning tools, see [SMS 2003 Software Update Scanning Tools](http://technet.microsoft.com/en-us/sms/bb676786.aspx). See also [Downloads for Systems Management Server 2003](http://technet.microsoft.com/en-us/sms/bb676766.aspx). System Center Configuration Manager 2007 uses WSUS 3.0 for detection of updates. For more information about Configuration Manager 2007 Software Update Management, visit [System Center Configuration Manager 2007](http://technet.microsoft.com/en-us/library/bb735860.aspx). For more information about SMS, visit the [SMS website](http://go.microsoft.com/fwlink/?linkid=21158). For more detailed information, see [Microsoft Knowledge Base Article 910723](http://support.microsoft.com/kb/910723): Summary list of monthly detection and deployment guidance articles. **Update Compatibility Evaluator and Application Compatibility Toolkit** Updates often write to the same files and registry settings required for your applications to run. This can trigger incompatibilities and increase the time it takes to deploy security updates. You can streamline testing and validating Windows updates against installed applications with the [Update Compatibility Evaluator](http://technet2.microsoft.com/windowsvista/en/library/4279e239-37a4-44aa-aec5-4e70fe39f9de1033.mspx?mfr=true) components included with [Application Compatibility Toolkit](http://www.microsoft.com/downloads/details.aspx?familyid=24da89e9-b581-47b0-b45e-492dd6da2971&displaylang=en). The Application Compatibility Toolkit (ACT) contains the necessary tools and documentation to evaluate and mitigate application compatibility issues before deploying Windows Vista, a Windows Update, a Microsoft Security Update, or a new version of Windows Internet Explorer in your environment. Security Update Deployment -------------------------- **Affected Software** For information about the specific security update for your affected software, click the appropriate link: #### Microsoft Visual Studio 2008 Service Pack 1 **Reference Table** The following table contains the security update information for this software. You can find additional information in the subsection, **Deployment Information**, in this section.| Inclusion in Future Service Packs | None |
| Deployment | |
| Installing without user intervention | VS90SP1-KB2669970-x86.exe /q |
| Installing without restarting | VS90SP1-KB2669970-x86.exe /norestart |
| Update log file | Not applicable |
| Further information | For detection and deployment, see the earlier section, Detection and Deployment Tools and Guidance. |
| Restart Requirement | |
| Restart required? | This update may require a restart. The installer stops the required services, applies the update, and then restarts the services. However, if the required services cannot be stopped for any reason, or if the required files are being used, this update will require a restart. If this behavior occurs, a message appears that advises you to allow the restart. |
| Hotpatching | Not applicable |
| Removal Information | Use Add or Remove Programs item in Control Panel. |
| File Information | See Microsoft Knowledge Base Article 2669970 |
| Registry Key Verification | HKEY_LOCAL_MACHINESOFTWAREMicrosoftUpdatesMicrosoft Visual Studio Team System 2008 Team Suite - ENUSP1KB2669970 'ThisVersionInstalled' = REG_SZ:'Y' |
Deployment Information
Installing the Update
You can install the update from the appropriate download link in the Affected and Non-Affected Software section. If you installed your application from a server location, the server administrator must instead update the server location with the administrative update and deploy that update to your system. For more information about Administrative Installation Points, refer to the Office Administrative Installation Point information in the Detection and Deployment Tools and Guidance subsection.
This security update requires that Windows Installer 2.0 or later be installed on the system. All supported versions of Windows include Windows Installer 2.0 or a later version.
To install the latest version of Windows Installer, visit the following Microsoft website:
For more information about the terminology that appears in this bulletin, such as hotfix, see Microsoft Knowledge Base Article 824684.
This security update supports the following setup switches.
| Switch | Description |
| /? or /h or /help | Display usage dialog box. |
| Setup Mode | |
| /q[n|b|r|f] | Sets user interface level n - No UI b - Basic UI r - Reduced UI f - Full UI |
| /quiet | Same as /q |
| /passive | Same as /qb |
| Install Options | |
| /extract [directory] | Extract the package to the specified directory. |
| /uninstall or /u | Uninstall this update. |
| /addsource or /as | Specifies the source path of the product msi. This option may be used when installing the update results in a prompt to insert the installation source media for the product. For example: <update executable> /addsource 'C:Product MSIVisual Studioenuvs_setup.msi' /addsource 'C:Product MSINetNetfx.msi' |
| Restart Options | |
| /norestart | Do not restart after the installation is complete |
| /promptrestart | Prompts the user for restart if necessary |
| /forcerestart | Always restart the computer after installation |
| Logging Options | |
| /l[i|w|e|a|r|u|c|m|o|p|v|x|+|!|*] <LogFile> | i - Status messages w - Nonfatal warnings e - All error messages a - Start up of actions r - Action-specific records u - User requests c - Initial UI parameters m - Out-of-memory or fatal exit information o - Out-of-disk-space messages p - Terminal properties v - Verbose output x - Extra debugging information + - Append to existing log file ! - Flush each line to the log * - Log all information, except for v and x options |
| /log <LogFile> | Equivalent of /l* <LogFile> |
| /sendreport | Send installation data for this update to Microsoft as a Watson report. No personally identifiable information is sent. |
| Inclusion in Future Service Packs | Microsoft Visual Studio 2010 Service Pack 1 |
| Deployment | |
| Installing without user intervention | For Microsoft Visual Studio 2010: VS10-KB2644980-x86.exe /q |
| For Microsoft Visual Studio 2010 Service Pack 1: VS10SP1-KB2645410-x86.exe /q | |
| Installing without restarting | For Microsoft Visual Studio 2010: VS10-KB2644980-x86.exe /norestart |
| For Microsoft Visual Studio 2010 Service Pack 1: VS10SP1-KB2645410-x86.exe /norestart | |
| Update log file | Not applicable |
| Further information | For detection and deployment, see the earlier section, Detection and Deployment Tools and Guidance. |
| Restart Requirement | |
| Restart required? | This update may require a restart. The installer stops the required services, applies the update, and then restarts the services. However, if the required services cannot be stopped for any reason, or if the required files are being used, this update will require a restart. If this behavior occurs, a message appears that advises you to allow the restart. |
| Hotpatching | Not applicable |
| Removal Information | Use Add or Remove Programs item in Control Panel. |
| File Information | For Microsoft Visual Studio 2010: See Microsoft Knowledge Base Article 2644980 |
| For Microsoft Visual Studio 2010 Service Pack 1: See Microsoft Knowledge Base Article 2645410 | |
| Registry Key Verification | For Microsoft Visual Studio 2010: HKEY_LOCAL_MACHINESOFTWAREMicrosoftUpdatesMicrosoft Visual Studio Team System 2010 Team Suite - ENUKB2644980 'ThisVersionInstalled' = REG_SZ:'Y' |
| For Microsoft Visual Studio 2010 Service Pack 1: HKEY_LOCAL_MACHINESOFTWAREMicrosoftUpdatesMicrosoft Visual Studio Team System 2010 Team Suite - ENUSP1KB2645410 'ThisVersionInstalled' = REG_SZ:'Y' |
Amtemu V0.9.2 Patch Download
Deployment Information
Installing the Update
You can install the update from the appropriate download link in the Affected and Non-Affected Software section. If you installed your application from a server location, the server administrator must instead update the server location with the administrative update and deploy that update to your system. For more information about Administrative Installation Points, refer to the Office Administrative Installation Point information in the Detection and Deployment Tools and Guidance subsection.
Ms12-021 Patch Download Torrent
This security update requires that Windows Installer 2.0 or later be installed on the system. Lol latest patch download full. All supported versions of Windows include Windows Installer 2.0 or a later version.
Pes Patch Download
To install the latest version of Windows Installer, visit the following Microsoft website:
For more information about the terminology that appears in this bulletin, such as hotfix, see Microsoft Knowledge Base Article 824684.
This security update supports the following setup switches.
| Switch | Description |
| /? or /h or /help | Display usage dialog box. |
| Setup Mode | |
| /q[n|b|r|f] | Sets user interface level n - No UI b - Basic UI r - Reduced UI f - Full UI |
| /quiet | Same as /q |
| /passive | Same as /qb |
| Install Options | |
| /extract [directory] | Extract the package to the specified directory. |
| /uninstall or /u | Uninstall this update. |
| /addsource or /as | Specifies the source path of the product msi. This option may be used when installing the update results in a prompt to insert the installation source media for the product. For example: <update executable> /addsource 'C:Product MSIVisual Studioenuvs_setup.msi' /addsource 'C:Product MSINetNetfx.msi' |
| Restart Options | |
| /norestart | Do not restart after the installation is complete |
| /promptrestart | Prompts the user for restart if necessary |
| /forcerestart | Always restart the computer after installation |
| Logging Options | |
| /l[i|w|e|a|r|u|c|m|o|p|v|x|+|!|*] <LogFile> | i - Status messages w - Nonfatal warnings e - All error messages a - Start up of actions r - Action-specific records u - User requests c - Initial UI parameters m - Out-of-memory or fatal exit information o - Out-of-disk-space messages p - Terminal properties v - Verbose output x - Extra debugging information + - Append to existing log file ! - Flush each line to the log * - Log all information, except for v and x options |
| /log <LogFile> | Equivalent of /l* <LogFile> |
| /sendreport | Send installation data for this update to Microsoft as a Watson report. No personally identifiable information is sent. |